In this month’s newsletter:
Nothing says Merry Christmas like a chunky upgrade to your favourite support software so this month we have started off focused on our Version 2 upgrade to the Data Protection Portal. Ho ho ho! 🎁🎅
There is also:
- a reminder of the seriousness of Cyber Security Threats and how you can best prepare for them including staff training;
- an update from the DfE that may impact data protection work as well as a few other stories that could have implications on data protection in schools;
- our partner spotlight highlighting a company we work with and recommend;
- the latest information on recent and current cyber threats;
- a previously asked question about handing out class lists to parents for the purposes of sending Christmas cards; and
- the latest on the new & updated resources in Global Documents since the last newsletter.
We have also created another staff guide for this month. The focus is on common breach risks (linked to email as that is the main vector for breaches currently) as well as some further cyber advice for staff. The more we can all raise staff awareness of these issues, the more we can reduce the risk for individuals and organisations.
As always, if you have any further questions about the topics below, or if you would like to book your next visit from us, either online using video conferencing or onsite, please get in touch via DPO@schoolpro.uk.
Don’t forget, if there is anything else that you need support with at this time, please ask and we will do whatever we can within our capacity to assist.
Stay safe and healthy!
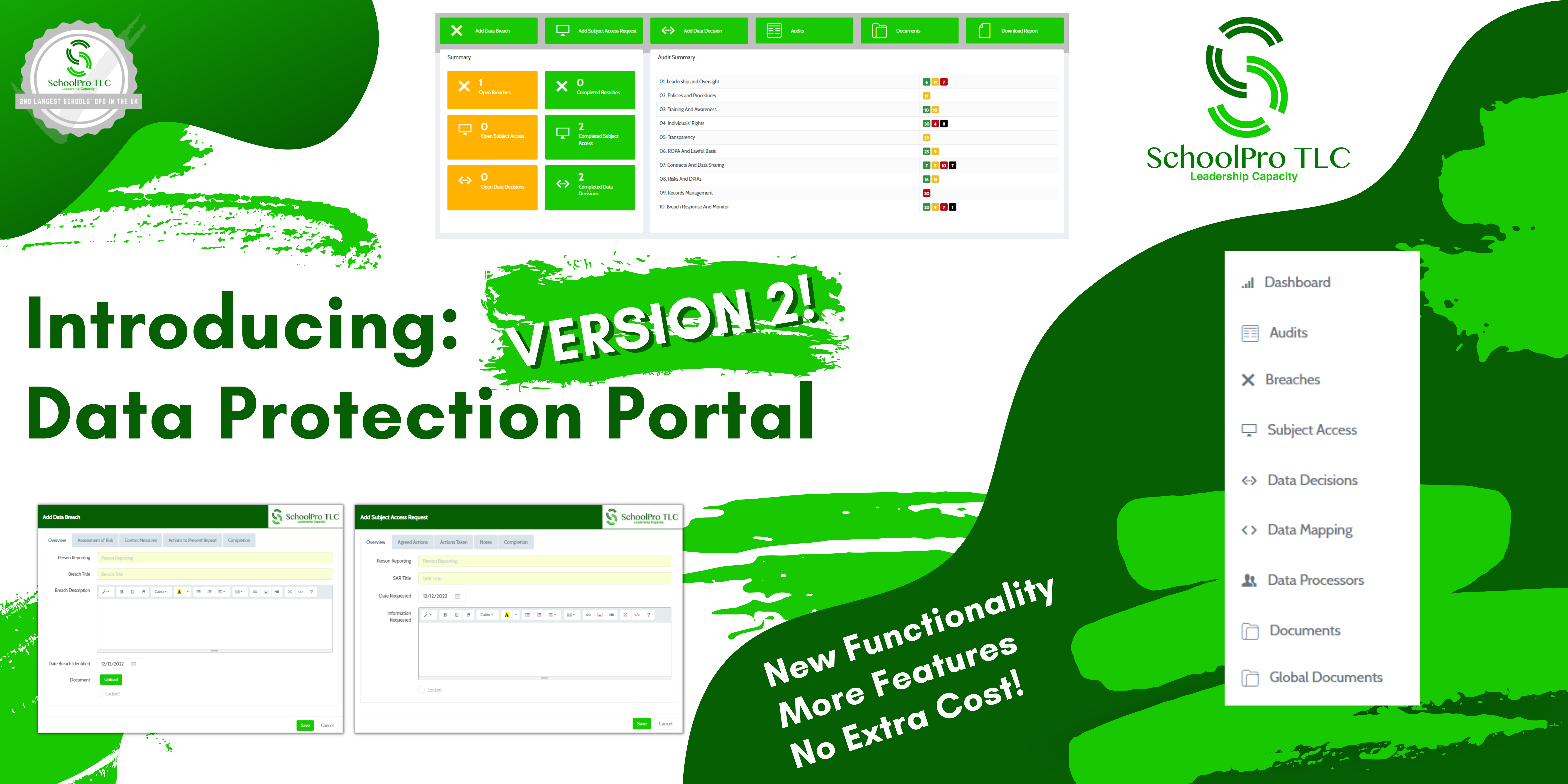
SchoolPro TLC Data Protection Portal – V2 Launch!
If you haven’t seen already, we launched our Version 2 upgrade of our Data Protection Portal earlier this week. We’re excited about it and we’re sure you are too. After all, it is Christmas and it is a time for giving!
Find out what we’ve given you here…
Staying Safe Over Christmas and into the New Year
Schools are experiencing cyber threats at an ever increasing rate from simple phishing attacks to more sophisticated penetration methods. We want to encourage all schools to reduce their risk as much as possible and this can be done at a technological level with your systems, as well as working with your staff and pupils to reduce their risk.
Cyber Threats
The risk of cyber threats can be reduced using simple but effective cyber hygiene practices including taking regular backups, using antivirus and keeping it updated, and being particularly careful with email security and not clicking on any suspicious links in emails. Staff training (as well as raising awareness) is also key to this and can be completed using our Cyber Security for School Staff training course (written by the NCSC) on our website.
Good password practice is also an important step for your staff and pupils. This includes using strong passwords (14 characters using a combination of letters, numbers, symbols, capitals/lowercase, or a technique such as combining three or four completely random words) and using different passwords for each system used. Not sharing passwords is also important and using multi-factor authentication, where possible, dramatically increases the effectiveness of security.
Last month, we highlighted parts of the Cyber security standards for schools and colleges | GOV.UK including the need to conduct a DPIA, ensure that you have at least 3 backup copies of your data, and, as we’ve mentioned before, make sure that staff are adequately trained in cyber threats.
Email Risks
We have published this advice before but it has been a while since we last did. Always worth a reminder:
- Check emails before they are sent so that you are less likely to make a simple error like using the wrong email address.
- Only use work email for work business. Never use personal email accounts or forward data to them.
- Password protect or encrypt files that contain personal information.
- Avoid emailing files internally. Save files in a shared area on either your internal server or in the cloud (depending on your organisation) and update the shared document.
- Avoid email for external communication where possible. Use alternative parental communication tools for example.
- Use Bcc when emailing an external group of contacts if you have to use email.
- Remove the auto-fill function in the address field so that the wrong email address isn’t populated by mistake.
- Add a short send delay so that the email stays in the Outbox briefly before sending and allowing you time to check and stop the email sending if you spot an error.
Data Protection and DfE Updates
Fewer updates from the DfE regarding data this month. The one that has come through is as follows:
- Share your daily school attendance data | GOV.UK
- How schools can share daily attendance data and access attendance reports.
- Update – information about when reports will be ready to view has been added under ‘Accessing your school’s attendance reports’.
Some other general data protection updates of note, however, are as follows:
- Data Protection Bill: Consultation to delay UK GDPR replacement | Techmonitor
- We have written before about the proposed data reforms and started to analyse the possible implications of these. As you can see, a further consultation is currently being planned which will further delay any reforms. We don’t know what the implications are of this additional consultation but we will be keeping across the information as it becomes available.
- Global data privacy regulators set resolution on facial recognition at annual meeting | Biometric Update
- Very few schools use, or propose to use, facial recognition as part of their processing. Biometric data is usually restricted to fingerprints for cashless catering or printing/photocopying. But facial recognition has been proposed in a few instances and it is possible that, over the next few years, use cases will increase. However, as stated in this article, regulators have agreed to a resolution regarding the use of facial recognition and the implementation of a set of six principles. This includes carrying out human rights assessments and assessing the “reasonableness, necessity and proportionality” of the processing.
- France says non to Office 365 and Google Workspace in school | The Register
- Whilst this is a decision that does not affect the implementation of these systems in UK schools, it is interesting to see this interpretation of the GDPR by a different supervising authority and how this impacts on the use of this technology in schools in that country. Germany has also stated it will ban Office 365 in schools. There is no indication at all at the moment that the UK is likely to follow suit but it is something that we will be keeping a close eye on for you…
- International transfers: empowering innovation and growth whilst protecting people’s personal information | ICO
- Since Brexit, the ICO has been looking at how international transfer mechanisms can be further developed. Recently, the ICO produced updated “guidance on international transfers. This includes a new section on transfer risk assessments (TRAs) and a TRA tool“
Partner Spotlight

Each month we throw the spotlight on a different partner. This month it is ShredPro.
ShredPro is a professional paper shredding company that offers a secure, efficient and cost effective shredding service adhering to the highest standards in the industry to ensure maximum protection of your confidential information.
Recent and Current Cyber Threats
NCSC Annual Review 2022
The National Cyber Security Centre (NCSC) has published its Annual Review for 2022 including topics such as ‘Threats, Risks and Vulnerabilities’, ‘Resilience’, ‘Technology’ and ‘Ecosystem’. You can read the full report here:
NCSC Annual Review 2022 NCSC.GOV.UK
How to assess and gain confidence in your supply chain cyber security
Useful guidance for Multi-Academy Trusts and large schools – practical steps to help medium to large organisations gain assurance about the cyber security of their organisation’s supply chain:
How to assess and gain confidence in your supply chain… | NCSC.GOV.UK
Choosing the right type of authentication methods
We would certainly recommend that organisations are looking to move away from just using passwords wherever possible and we know that many schools and Trusts are already implementing multi-factor authentication. Here are some recommended authentication models for organisations looking to move ‘beyond passwords’:
Authentication methods: choosing the right type | NCSC.GOV.UK
Recent Threats Identified…
- LastPass Data Breach – Password app company LastPass has reported a second data breach that may be related to a previous breach in August where source code and some proprietary LastPass technical information were taken. The company has reported that in this most recent attack, a threat actor using information from August’s attack accessed “certain elements of our customers’ information.” LastPass says, however, that customers’ passwords remain safely encrypted, its services remain fully functional, and it is currently working to discover the scope of the attack and what information has been accessed. The advice from LastPass is to follow its best practices around setup and configuration of LastPass as detailed here: How to Set Up Your New LastPass Account | The LastPass Blog.
(Cheltenham IT Support | Reform IT) - Massive WhatsApp Data Breach – According to a Cybernews report, it has been alleged on a hacking community forum that 487 million WhatsApp user phone numbers from 84 countries, including the UK, are for sale online as part of a database which may have come from a breach. It’s been reported that the UK dataset contains the phone numbers of 11 million users and is being sold for a per-capita sum of $2,500. The advice is, if you need to check whether your number or email has been stolen in a breach, use a site like Have I Been Pwned: Check if your email has been compromised in a data breach. To make accounts more secure, choose strong passwords, don’t share them between accounts, use 2FA where possible, and use a good authenticator app.
(Cheltenham IT Support | Reform IT) - Phishing Threat in Microsoft Customer Feedback Tool – Researchers have warned that threat actors could send a phishing email through Microsoft’s Dynamics 365 Customer Voice CRM tool. This could be done by disguising it as an important voicemail from the customer where the “Play Voicemail” button redirects the victims to a phishing landing page. The advice to users is to look carefully at all URLs, even when they are not in an email body.
(Cheltenham IT Support | Reform IT)
Previously Asked Question
We are asked data protection questions by schools on a daily basis and there are some questions that come up regularly. We now have an FAQ section on the website for these and all of our answers are published there. You can find this on the Data Protection page of the website or in the blog. As it is relevant for this time of year, and we are still being asked this even this close to Christmas, here is a classic question. We will publish more in future newsletters:
Should we send out Christmas card lists to parents with names of the children in a class/group/year?
Answered December ’20.
From a pure data protection point of view, giving out the names of the children within a class or year group to all of the parents is not a good idea if they haven’t given consent. Whilst a first name on its own might not seem like a lot of data (because it isn’t), it can then be matched to the year and class of the child and someone could start to build a picture (even if it is a very blurry one at this point). And it only takes one parent to complain that they didn’t want their child’s name given out for the school to have to answer some awkward questions. Here are some alternative ideas though:
- Add a line on the consent form regarding sharing a first name only with other members of the class/group etc for the purposes of Christmas/Birthday lists when the child joins the school or at the start of the year. Not helpful at this point for the current cohorts we realise but useful for next year onwards.
- Ask consent at this point. This may not be practical depending on the size of the classes but it could be as simple as the class teacher asking parents that they are happy for their child’s name to be on the list as they pick their child up at the end of the day and ticking them off. Or, if the school is using online solutions for communication with parents, putting the question out on that or posting a poll for them to complete.
- Finally, the other thing a lot of schools are doing now, is they are getting the parents to collate the list between them. Then it is the parents that are giving each other the children’s names and not the school at all. Some parents have done this by creating a sign up sheet to go on the outside of the class door so parents add their child’s name at pick up time and then the list is circulated by one of the parents. Others have parents that setup WhatsApp or Fb groups for the other parents in their class and they share the children’s names that way.
New & Updated Resources on the Portal
Since our last newsletter, we have added 9 new documents and updated 1 document:
New Documents
- DPIA – Blank Template – Short Version
- This is a new blank template that is ideal for processors that require a DPIA (for example, are subject to the Children’s Code as an online system provided by the school) but only process limited or ‘low risk’ data.
- DPIA – Lexonik
- DPIA – Weduc
- Guidance – Right of Access (Guide to Subject Access Requests) – ICO Guidance
- Guidance – Surveillance Camera Code of Practice
- Letter – FOIA Acknowledgement Template
- Letter – FOIA Response Template
- Letter – SAR Acknowledgement Template – Extension Notification
- SAR Checklist
Updated Document
- DPIA – Blank Template
- Template refined for use with ‘medium’ risk processors – easier to complete for schools and trusts.
Data Protection in the News
When did our phone numbers become the new identifier du jour? | IAPP
Twitter confirms vulnerability exposed data of anonymous account owners | Engadget
Twilio customer data exposed after its staffers got phished | The Register
Slack exposed hashed passwords for years | The Register
Mozilla: 18 top reproductive health apps share your info | The Register
Ransomware attack on a UK water company clouded by confusion | The Register
Twitch Confirms Massive Data Breach, Said a Hacker Accessed Company’s Servers | Crossover 99
Tech News : Major NHS Supplier Hit By Ransomware Attack | ReformIT
Facebook and Instagram apps can track users via their in-app browsers | Engadget
Edtech companies breaking UK data laws, privacy campaigners claim | Financial Times
Former health adviser found guilty of illegally accessing patient records | ICO
Most hacked passwords revealed as UK cyber survey exposes… | NCSC
Gloucester Council planning site still disrupted from cyber attack | BBC News
Manx Care faces £170k fine over patient data breach | BBC News
Instagram fined €405m over children’s data privacy | BBC News
Classroom app Seesaw abused to send ‘inappropriate image’ | The Register
If you have any other questions about this or any other data protection topic, please contact us at DPO@schoolpro.uk.
Stay safe and healthy,
The SchoolPro TLC Team
SchoolPro TLC Ltd (2024)
SchoolPro TLC guidance does not constitute legal advice.
SchoolPro TLC is not responsible for the content of external websites.